The goal of DiTiNOW project is to provide a low cost, low latency and easy to use anti-counterfeiting solutions for consumers and brand owners.
Counterfeiting is a "double spending" problem of real world assets. It is not acitvity of an asset being sold multiple times, instead it is the AUTHORIZATION of the asset being fake or replicated. A product authroized by brand owners must be genuine, however a genuine product may not be authorized. Overruns by OEM factory, defective, damaged, stolen, contaminated,expired goods are examples of real/genuine but nor authorized products.
Cases about "genuine but not authorized products" can be find here and 这里. The first case was selling of expired product which should be trashed, in the second case genuine goods was repacked with a design never approval by brand owner. For both cases the product were real/genuine but not authorized, nerver the less defendants' action clearly violated the rights of brand owners.
Traditional definition of counterfeit goods are fake or replica of real product. As we can see from cases above, this definition limits our vision on how to fight against counterfeiting. The focus has to shift from what is "real/genuine" to what is "authorized". (By tradition definition, counterfeit goods is neither genuine nor authorized.)
The latest approach to prevent counterfeiting is blockchain based, decentralized, distributed title recording protocol. Brand owners can uses this protocol to tokenize AUTHORIZATION into NFT for every item they authorize to built or sell. Consumers can verify the source of authroization and legitimate owners of an authorized product simply by few touches on thier smart phone. System built on this protocol featuring low cost, low latency and privacy protecting, thanks to blockchain technology and NFT. We would likt to call this new type of title recording protocol as Digital Title, thus the the project name DiTiNOW come from.
The solution offer by DiTiNOW project includes:
- A web based application CryptoC14.com (for demostration please visit DiTiNOW.com/diti)
- A POS public blockchain (CC14 chain)
- HTTP service is needed for distributing title token (aka NFT, acting as certification of authenticity/ownership) and providing non-transactional information, such as product information and designated wallet information.

【COMPLETED LIST】
- (2019) Proof of concept
- (2020 ~ now) MVP CryptoC14 - the main application
- (2021) CC14 public blockchain - a NXT clone
【TO DO LIST】
- Documents - how-it-works and how-to
- Migrate product image from HTTP server to IPFS.
- Impletment the solution on Solonan
- Multi language UPC database
- Improve shared wallet security
- Support NXT main and test net
- Support Ardor main and test net
- Finalize service process with title token
- Finalize return process with title token
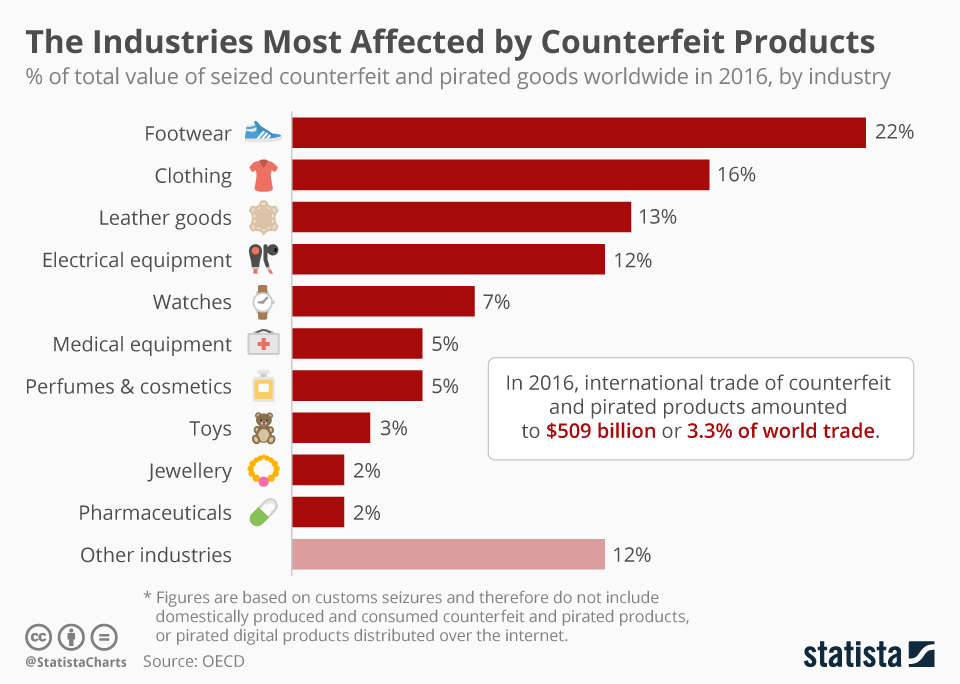
In 2016, international trade of counterfeit and pirated product amounted to $509 billion, or 3.3% of world trade. (That is one in every 30 dollars!)
Terms and defination - with Blockchain based proof-of-ownership protocol
Authentic product : consisit with three parts:
- Title Token - a NFT issued by IP owner for every item authorized to build/sell. (NFT issued by non-IP owners are just a Non-Fungible Token)
- Physical object - materialized NFT, manufactured per IP owners' specification, found in NFT metadata
- Data label - bridging crypto asset to physical asset. DiTiNOW suggest use QR code to store title token ID, which should be use as product ID as well
Counterfeit product: unauthorized product, product without Title Token, the crypto version of certification of authenticity/ownership
Authentication element: title token store on blockchain, interconnect to physical world by data label, normally product ID = NFT ID.
Note: Title token is the true authentication element, not the tangible data label. Data label is just storage media for token ID, which can be store on data media such as QR code, RFID and NFC chip, even hand written.
Terms and defination - Traditional:
Authentic product: material good produced under the control of the legitimate manufacturer, originator of the good or holder of intellectual property rights.
Counterfeit product: material good imitating or copying an authentic material good
Authentication element: tangible object, visual feature or information associated with a material good or its packaging that is used as part of an authentication solution.
Blockchain based proof-of-ownershio protocol use NFT to tokenize the certificate of Authenticity/Authorization of a property. The token can represent the authenticity and the ownership of a piece of artwork, comcial products or simply an idea recorded.
Anti‐counterfeiting logic: product with title token issued by brand owner is authentic/authorized; otherwise fake/unauthorized. (The anti-counterfeiting logic on how NFT can prevent counterfeit is demostrated on video above.)

Shown above, two physically non-distinguishable products sold by two stores, the red shop to the right is selling authentic good. Blue shop to the left failed to provide the certification of authenticity, the crrosponding NFT, is selling fake.
- Tokenized certificate for every object with title token, aka NFT minted by brand owners.
- Product status determined by wallets addresses where the title token is parking. Every brand owners designated and publish their own wallet address.
- Zero knowledge proof of title token redemption process
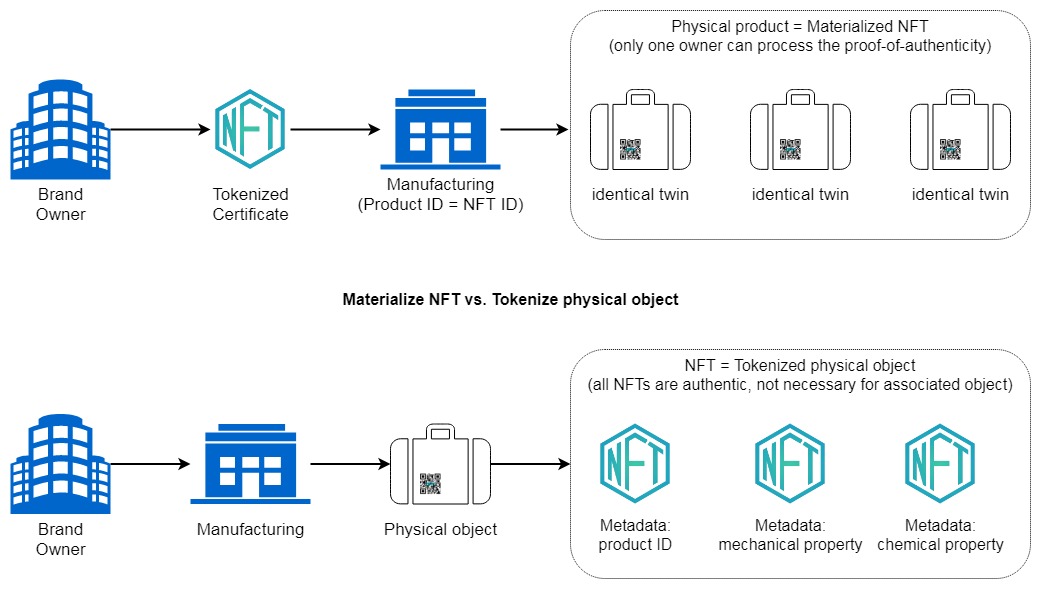
【Materialize NFT】 current manufacturing process doesn't need to be modified other than how the serical number/product ID is generated. Brand owner need to tokenize their authentication by using NFT, factory will use NFT ID instead of existing scheme of serial number/product ID. The quantity of authorized product is limited by how many NFT issued by brand owers instead of how many physical goods manufactured by OEM factories.

As demostrated in video above, no matter how many existing replicas with identical physical and chemical characteristics, there can be one and only one set of authorized combination of NFT and pshycial object with matching ID. Even for brand owners' the chanes of issuing two NFTs with same ID is less than 264, which is less the chance to win three super lottery.
Note: Materialized NFT is different from tokenize physical object with NFT. Since anyone can tokeize a physical object by metadata some aspect of the object. E.g. serial number, DNA sequence, quantum state, detailed physical description, etc... such NFT may issued by object owners instead of IP owners, however the origin of authenticity can not be proven with such NFT.
【Labeling】 CryptoC14 use two QR code for each physical object, a Title TokenID and Verification code.

- Title Token ID: a public accessable data label found on product package and afixed to physical object. It allow recipients to perform authentic check before accept the item. Manufactures should choice between short or long format depends how much real estate space available on product label.
- Verification code: data encrypted from title token ID by using AES, normally store in a consealed data label access by paid consumers only (think of scratch off lottery tickets). Consumer use matching pair title token ID and verification code to redeem the title token (NFT).
Manufacturers can use other data media type to store the code, for example RFID or NFC chip. DiTiNOW recommend QR code for low cost production and allow remote access to the data store on the label, benefitting today's e-commerce.
【Supply Chain】 Downstream process does not require any modification, since during the entire product stream only brand owner and consumers get in touch with title token (NFT). The return process need some training, since the roles of recipient and provider reversed in return, extra caution needed to handel the title token transaction. (Documents on return/exchange/post sale services process is WIP.)
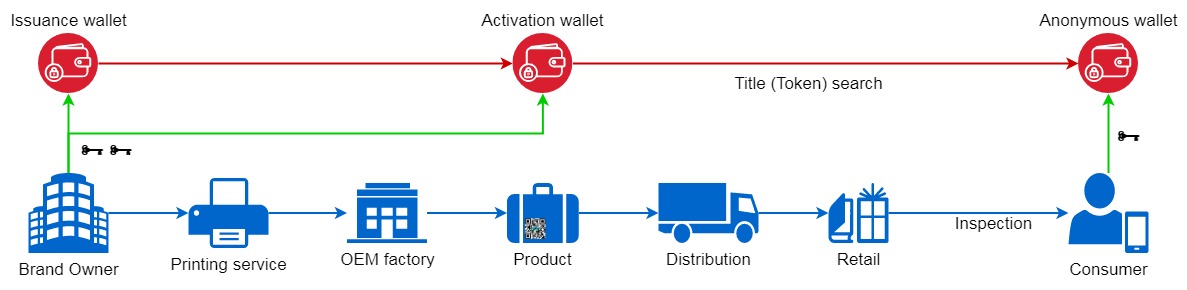
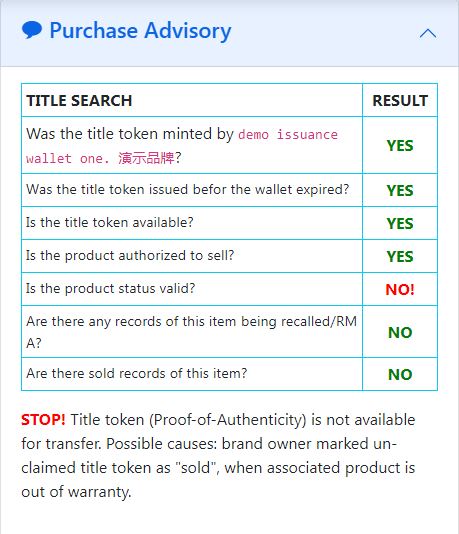
【Shopping】 The shopping process require an extra "Title (Token) search", check for authenticity and ownership of the product. Consumer not only performing a physical inpsection on the targeted object, they also need to perform a "title search" to make sure the object under investigation has clean title. Once paid and received the physical object, consumer can discover the verification code and use it along with title token ID (product ID) to redeem the title of the object. Similar process are found in real estate and automobile transcation. Tradtional tittle search are expensive and long wait time, not suitable for daily shopping activity. Blockchain based title search, on the other hand takes no more than few seconds and no fee for consumers. Details on using CryptoC14 dApp to perform title search and redeem title will be cover by How To.

Note: consumers is define as recipients of the product. The authenticity of a product may not be the top priority of a end consumer, but it will be one of the top priority of distributers and retailers, either receiving of new product or accepting return from end consumers. To avoid the penalty for distributing/selling of counterfeit good, recipients should perform a title search when there are any doubts regarding the product/vendors receiving.
【NFT based title search】The status of a NFT and associated physical object is determind by the wallet where NFT is parking, the wallet assigment is designated by brand owners. Any unassigned/unknown wallet is consider as belong to end consumers.
| Wallet address | Company | Designate function |
|---|---|---|
| CC14-49CE-CXZZ-3QHW-AH4JK | DiTiNOW/CryptoC14 | Validator - DiTiNOW official wallet to validate all other wallet |
| CC14-5KKJ-TXML-FKM3-4SLZB | DiTiNOW/CryptoC14 | Issuance - for tokenize authorization |
| CC14-DUPL-QDTD-ZGDJ-7YJTW | DiTiNOW/CryptoC14 | Activation - for activating product |
| CC14-6LFR-HCTG-F2LR-87ZB4 | DiTiNOW/CryptoC14 | Services - for post sale services |
| CC14-CWWS-4MHT-ZKHY-DGUYC | DiTiNOW/CryptoC14 | Return - for authorized returing |
| CC14-85CR-6PAZ-SL4Y-CUCDA | DiTiNOW/CryptoC14 | Authorized Retailer - a retailer who want to handling title token |
| CC14-9QS5-MBBX-56MF-ESNEB | DiTiNOW/CryptoC14 | Dumpster - for defective, stolen, lost, damaged, contaminated products |
| CC14-XXXX-XXXX-XXXX-XXXXX | anonymous | Marked as SOLD |

Consumers can find the title search summary in CryptoC14 ->【Authentication Check】 -> 【Purchase Advisory】
【Requirement】
- HTML 5, CSS, Javascript, PHP
- jQuery 3.5.1, bootstrap 5, Crypto-JS 4.1, NRS 1.12.2(Nxt Reference Software)
- Chrome, Firefox
- apache 2
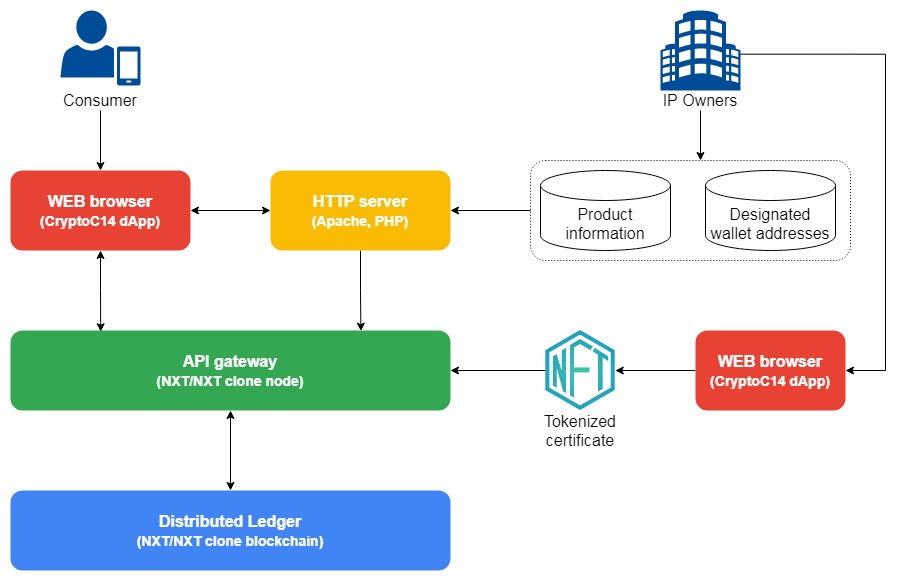
CryptoC14 uses data from four sources. Product information, product images, designated wallet address and the ledger of tokenized certificate, aka NFT. The first three data set are used to interpret what the NFTs are about and display images for it, the data sets is be offer by brand owners' http server.
【Product Information】 A example of product information shown below. Please pay attention to the address of "noFakeUrl", application will find out the validation wallet address trusted by your company and the PHP script at this location.
【Product Image】 Image files are named after the product barcode follow by -#.jpg, E.g. 6901234567890-1.jpg , this allow the application to perform a slide show for given barcode.
【Designated Wallet Address】 The designated wallet address includes two parts, a validationCode and the wallet information. The purpose of validation code is allow brand owner to proof the integrity of the wallet information. For example, all designated wallet addresses by DiTiNOW demostration was validated by DiTiNOW's offical wallet address CC14- 49CE-CXZZ-3QHW-AH4JK. Counterfeiters may set up an fake anti-counterfeiting web site and assign their own wallet addresses. However, counterfeiters cannot validate the wallet information by using target brand owners' offical validation wallet address, unless they hacked into that wallet. The tool to validate wallet information can be access at 【CryptoC14】 -> 【Crypto Evidence】 -> 【Validate Wallet Information】.
Brand owner are responsible to host and share their own designated wallet address book and make publick announcement of their offical validation wallet. This is the whold idea of decentralized, distributed title recording protocal about, brand/IP owner souldn't and doesn't need third parties to validate what they are authorized/trusted.
【Ledger of NFT】 Ledger of title token (NFT) are stored on CC14 public blockchain. Example and required metadata to issue a title token are shown below:
- "name" - 3 to 10 alphanumeric characters. Since barcode are normally 13-digis, it will be conver to base 32 in order to fit in. E.g.
68r8q52mi(base32) <-> 6901234567890(decimal). - "description" - this filed will determind the product ID, if it display as
NFTID#####, then the physical object shoud use title token ID as product ID. Otherwise an existing pruduct ID/serial number will be display here. Please ignore the#####follow by NFTID, it just a placeholder and has no significant meaning. - "quantityQNT": "1" & "decimals": 0 - indicate one unbreakable token, in other word a NFT.
【CryptoC14 dApp】 Detail instruction on how to use CryptoC14 dApp will be covered by 【How To】.
【HTTP server】 CryptoC14 can run from all major browser without installation/configuration. However, brand owner might want to set up a HTTP server to share their designate wallet addresses book and offer an unattendant NFT redemption services. A standard Apache 2 with PHP/OPENSSL support is needed for the services. Detail instruction on how to install CryptoC14 dApp will be covered by following topic: 【installation CryptoC14 web application】.
【API gateway/blockchain node】 Please visit github/ditinow/cc14 for detailed instruction.
Serverless - for Tokenize authorization
w/ HTTP server - for Authentic check and Title token redemption
【Tokenize authorization】
Title token can be issue with CryptoC14 runs from Chrome or Firefox broswer without http services, as long as there is internet connections and gateway throught one of the blockchain node.
- Visit github/ditinow/diti and clone the rspository.
- Use your favor browser to open and bookmark
index.html - Create and assign wallets functions, such as title token issuance, product actication, services, return and dumpster. The list of designated wallet should save to myAddressBook.js.
Where
"walletAssignment"can be one of following:- Validator: assigned to to validate all other wallet address, please use 【Validation】 tool to generate validation code for all designated wallet addresses. Note, validator is self validated.
- Issuance: designated for issue title token, aka NFT minted by brand owners.
- Activation: authorize product for sell.
- Services: company's park space for all products authorized for post sale services, such as recall, repair.
- Return: park space to handel return/exchange. (Return process is currently WIP)
- Dumpster: designated for defective, damaged, lost ... products. The purpose is to prevent the title token being use by counterfeitor.
- Define more wallet function as needed.
- Create product information list. This list should save to myAssetBook.js.
- Product image shoud save into directory
diti/images/products/. Product image should named as#############-#.jpg, the first groupt of#is 13 digits barcode of products,-#is the number sequence of product images. CryptoC14 product slideshow support upto 3 images. - Generate and store the AES eccryption
key和ivinto doNoShare.js . This is the key and iv needed for encryption and decryption the verification code, used for the unattendant title token redemption process. "doNoShare.js" should not be uploaded into pbulic web site. If your company use secure printing service to product the verification code package, the verification can be generate with hardware key instead, thus there is no need to store the key and iv in intranet. - Get some CC14 token and your are ready to issue title token for your products.
【Authentic check and Title token redemption】
Consumers and law enforcment need access to your company's myAddressBook.js and myAddressBook.js inorder to interpretate the blockchain record. The same github/ditinow/diti rspository can be part of your company website, minus the "doNotShare.js" file. The installing directory should be part of product information, show as "noFakeUrl":"http://www.YourBrandName.com/diti/".
Inorder to provide unattendant title token redemption services, company web server runs PHP scripts to perform the task.
The requestTitleToken.php needs to include th API gateway URL and the passphrase of the activation wallet. Pre-defined AES key and iv for decrypt verification code is also included.
Note. web administrator has the encryption information and the passpharse of the activation wallet, however, he will not be able to fake title token, since only the NFT issued by designated ISSUANCE wallet is consider as valid title token.
For validate the verification code only, the validateTitleToken.php include AES key and iv, but the passphrase. No blockchain transaction will be occured. This tool is for law enforcment and recipients other than end consumers to validate the verification code without take ownership of the title token.
CC14 is a POS public blockchain cloned fron NXT. For detail instruction please visit github/ditinow/cc14.
System requirement:
- Hardware: 1 CPU, 2GB system RAM
- OS: Windows 7 or above; Linux
- Java: 8, 11
In throey we can built a consumer product title recording system offering services similar to vehicle resigstration system and vehicle history reports system (e.g. CARFAX). Such system works very well to prevent a salvage title vehicle faked as a new car. The system is also the reason there are many of counterfeit auto parts, but no counterfeit cars.
Anti-counterfeiting technology can be classfy into three categories: proof-of-ownership, physical, track & trace
【Physical technology】 are make by manufacturing processes and/or material identification, secure labels such as laser stick, water mark, etc. Common defects of physical thecniques are:
- Unable to explicitly identify the source of Authorization.
- Due to global supply chain, manufacturing processes, materials and labels are wildly available to all, includes counterfeiters.
- Brand owner have to continuely invested into new hysical techniques to stay in the race.
- In order to propertily identificate counterfei goods, consumers need to update their anti-counter knowolodges. Counterfeiters normally can take advantage of consumers.
- Dedicated and expensive tools might be needed for manufacturing processes and/or material identification.
【Track & trace technology】 verify authentic products by trace back to it's origin, normall done digitally via supply chain data. Common defects of physical thecniques are:
- No clone proof. Cloned secure label extraced to identiacl offical track & trace data.
- Weak anti-counterfeiting logic, sometime caused backfire. Some track & trace provider couunt number of secure label being scanned to identify if there is counfeiting.
If a single set of secure data being access more than one times, then a potential counterfeiting warning will be given.
- There is now way to tell if the 1st, 2nd or 3rd scan was performed on a potential counterfeiting good.
- Repeating scans can caused an authentic products being marked as a potential counterfeiting.
- Vast amounts of data. Except the information about origin and status of seller, most of trand & trace data are not important to identify counterfeiting goods.
- Adaptability. Data collecting are one the most expentive part of big data. Track & trace require no only the brand ower, but also all entities involved in supply chain to collect data. Hardwear, softwear and trainging cost by thirty parties are big contirbution to the success of track & trace solutions.
| PHYSICAL TECHNIQUES | TRACK & TRACE | PROOF-OF-OWNERSHIP | |
|---|---|---|---|
| MEDIA | laser label, material investigation ... | QR code, RFID... | QR code, RFID... |
| TOOLS | bare eye, specialized equipment ... | smart device | smart device |
| SKILLS NEEDED | YES | NO | NO |
| SUSTAINABILITY | NO | YES | YES |
| DATABASE | traditional | traditional, blockahain | blockchain |
| FAKE PROOF | NO | case-by-case1 | YES |
| CLONE PROOF | NO | NO | YES |
| ANTI-COUNTERFEITING LOGIC | outdated | weak, backfire | strong |
| ADAPTABILITY | easy | complex | easy2 |
| NFT(Non-Fungible Token) | Title(property) |
|---|---|
|
Exclusive possession Exclusive use and enclosure Acquisition Conveyance |
Exclusive possession Exclusive use and enclosure Acquisition Conveyance |
| Sender wallet address | Grant deed: grantor |
| Recipient wallet address | Grant deed: grantee |
| Unique NFT ID (afixed on consumer good) |
Unique legal description (of the real property) |
|
NFT history search Digital signature, timestamp Record by blockchain |
Title search Notarize Record by trusted agency |
- What happened if the secure code is leaked?
- How do consumers protect their privacy, since this technology us "proof-of-ownership"?
- Can counterfeitor fake a secure code?
- Do consumers need to visit multiple sites for their shopping need?
- Can this method prevent counterfeitors from return fake unit to brand owner?
- How does a NFT bundle to physical object?
- How does a counterfeit good with cloned secure code being identified?
- Can proof-of-ownership detect "new wine in old bottle?
- How to prevent counterfeitor setup an fake website for authentic check?
- Both Proof-of-Ownership and track & Trace use QR code, how can consumers distinguish them just by look at the label?
- How much dose Proof-of-Ownership cost?
- How does CryptoC14 answer to social engineering attach?
- Does CryptC14 collect any user data?
Q: What happened if secure code were leaked?
A: Secure code, aka NFT ID, is a public infomation since the time when it was generated on CC14 blockchain. Proof-of-ownership technology doesn't count the number of time secure code being scanned, a "leaked" secure code has no affect on this technology.
Q: How do consumers protect their privacy, since this technology us "proof-of-ownership"?
A: Ownership is proven by sucessfully control the CC14 wallet where the NFT is parked. For example user can digitally sign a arbitrarily message by generating a message token to prove the ownership of a wallet. There is no private information to be collected, other than wallet address/publick key. Consumers can defragment the purchase pattern by using multiple CC14 wallets for NFT collections.
Q: Can counterfeitor fake a secure code?
A: No. The issuer information can not be tamper.Q: Do consumers need to visit multiple sites for their shopping need?
A: No. CryptoC14 maintain a master list of designated wallet addresses for all company using the CryptoC14 solution. Each wallet address record is verified and digitally signed by brand owners.
Q: Can this method prevent counterfeitors from return fake unit to brand owner?
A: Yes/No. The returned physical object may not be the same one, however the Proof-of-authenticity is the original one. That means if buyer return an idential replicate with corrsponging title token, then the one he keep will lost the proof-of-authenticity, thus a fake.
Q: How does a NFT bundle to physical object?
A: Ideally the physical object should use NFT ID as product ID/serial number. We can virw the manufacturing process as materialize of a NFT. The amount of NFT minted by brand owner determind the amount of authentic physical objects. By comparison, other solution provider tokenized existing physical object using NFT. Depends on the aspect issuer choice to mint the NFT, E.g. serial number, description of phsyciacl property, etc. All NFT minted after the physical object manufactured can be authentic, this will give replica a chance to pair with a authentic NFT.
Q: How does a counterfei good with cloned secure code being identified?
A: Product without crrosponding NFT are fake. IF seller can not proof he owns the crrosponding NFT, then try another seller.
Q: Can proof-of-ownership detect "new wine in old bottle"?
A: Wine and cosmetics beening attacked by "new wine in old bottle" the most. Since all sold record is permanently written into block, if a vendor stock high percentage of previously sold products, and the NFT issuance and product activation date has wide range, then this vendor may not be trustworthy, sinc the authentic NFT may be reused.
Q: How to prevent counterfeitor setup an fake website for authentic check?
A: Every designated wallet address will be verified and digitally signed by brand owners. We strong recommend every brand owner use "/diti" as official anti-counterfeiting web site, such as http://YourBrandName.com/diti/ . Also, please use button under 【Authentication Check】 -> 【Issuer Information】 to verify the integrity of designated wallet information. Counterfeiter may setup a fake anti-counterfeiting web site, however they cannot fake the issuance information of NFT, unless somehow they got the fake issuance wallet validated and digitally signed by brand owners.

Q: Is the anti-counterfeiting solution offer by CryptoC14 complex to adapt?
A: No.
Q: Can data be modified?
A:
Q: What is the different between Secure Code, NFT ID, and Registration Code?
A:
Q: Can registration code been re-use?
A:
Q: Do brand owners, law enforcment, and consumer need to setup an account in order to use proof-of-ownership technology offered by CryptoC14?
A:
Q: Is thers vulnerability on this technology?
A:
Q: Both Proof-of-Ownership and track & Trace use QR code, how can consumers distinguish them just by look at the label?
A: Verify via CryptoC14.com.
Q: How much dose anti-counterfeiting solution based on proof-of-ownership/authenticity cost?
A: CryptoC14 is an open source project, the application is free to use. The blockchain transcation is paid in CC14 token, which is also free to obtain.
Q: How does CryptoC14 answer to social engineering attach?
A: Primary social engineering attach target are designated wallet passphrase and verification code uses for title token redemption process.
-
Wallet passphrase security
Wallet passphrase security should apply company password handling guideline. Designate wallet are normally share by operators during real production. For example, an insurrance wallet for a well known brand may operator by serveral operators to server manufacturing. Having operators access to the plain text wallet passphrase is very risk. One solution is encrypted the plain text wallet passphrase by personalized AES key and iv.
Personalized key and iv, safekeeping by individual iv hash (operator ID) key hash (operator secret) Wallet access c6b0f675a3f8e4a84a95e89a81a4cf4e 5aa6652490eed814f1d525fb0df07301 CC14-5KKJ-TXML-FKM3-4SLZB 7983137cb0ab651f26438228274fa266 43acefa6295436c4b753b98ee1c22490 CC14-5KKJ-TXML-FKM3-4SLZB c6b0f675a3f8e4a84a95e89a81a4cf4e 5aa6652490eed814f1d525fb0df07301 CC14-UEM4-XQBX-HZWW-G2FNW Credential List, safekeeping by scripts iv hash (operator ID) Wallet access Encrypted wallet passphrase c6b0f675a3f8e4a84a95e89a81a4cf4e CC14-5KKJ-TXML-FKM3-4SLZB nQTZgPj9X/6pwNeLNnkbDHzBdhm1zrtE+eQgNFgIwaEqTjodg1BtNteSfhjjj2OizxCFxXOXTdoU+YPtQydfmA== 7983137cb0ab651f26438228274fa266 CC14-5KKJ-TXML-FKM3-4SLZB hlbELV+RoOi0Vv+6pgHjj7FYYe5A1WZq0rwLYbrw/5zZ6HH5547ZJkRjUpXFUcsdhaI0cdSVaYXm7Jq6sw+92Q== c6b0f675a3f8e4a84a95e89a81a4cf4e CC14-UEM4-XQBX-HZWW-G2FNW 1vDrN0iQsyZnQ+ZRb6Q1b5gusYy0gw2TueYwhDLaqUFteyQs0lrH89DIbHd8PsKjIQD+BhK8e8RY+nUcHkOqWg== With personalized encrypted wallet passphrase, neither operators nor system administrator has the original wallet passphrase. A process demostrated at Shared Wallet .
-
Verification code security

Verification code Verification code is encrypted from NFT ID by AES algorithm with key and iv konwn by brand owners only. The code will be used by end consumers for the unattendant title token (NFT) redemption. Mishandling of verification code can cause lost of title token, the sole proof-of-ownershi/authenticity. Verification code must be develiable and remain sealed until end consomer ready to claim title token.

Social engineering attack Secure printing service shoud be use to produce the verification code label, the code should be generate in system memory by brand owners supplied encryption key and iv. chance for insider to get large amount of valid verification code is very low, since he either get on hold of the encryption key and iv, or he have to physically damage the code label package in order to extract the data.
Counterfeiters also need to race the replicas to recipients (distributors, retail stores, end consumers) before the product status changed. For example if the consumer claim the title token, then the product will be marked as SOLD; brand owners can also marked product associated with un-claim title token as SOLD. If seller cannot deliver the title token for a SOLD item, that means seller is not the ture owner of the authentic item.
Q: Does Crypt0C14 collect any user data?
A: No. No users data will be collect and transfer to CryptoC14. CryptoC14 does utilize browser's localStorage to store user datas to save some typing. LocalStorage can be review by 【Right click browser empty space】->【Inspect】->【Application】->【Storage】.
Note: CryptoC14 recommend user to built their own CC14 API gateway instead of using public gateway.